PXE Boot, What is PXE? How does it work?

PXE Boot – Introduction What can you expect to learn about PXE from this post? High level overview of PXE boot process. Use cases for PXE boot. Detailed end to end overview of the PXE boot process. Technical details of each stage. What is PXE? In this post we are deep diving into PXE boot. […]
Raspberry Pi PXE Boot – Network booting a Pi 4 without an SD card
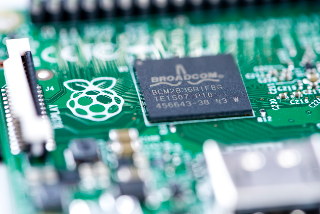
What does this Raspberry Pi PXE Boot tutorial cover? This Raspberry Pi PXE Boot tutorial walks you through netbooting a Raspberry Pi 4 without an SD card. We use another Raspberry Pi 4 with an SD card as the netboot server. Allocate 90-120 minute for completing this tutorial end to end. It can faster if […]